We use cookies on this site to
improve your browsing experience, analyze individualized usage, and
website traffic tailor content to your preferences, and make your
interactions with our website more meaningful. By clicking "Accept All" closing this banner, or continuing to browse this site, you
consent to the use of cookies.
-
Products
-
Solutions & Technology
-
Services & Support
-
Resources
-
Company
-
Customer Portal






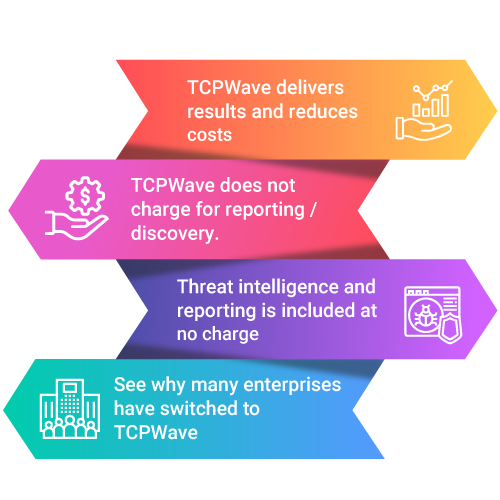














 TCPWave's DDI reporting capabilities
have revolutionized our organization's performance. The swift
generation of customized reports on DHCP and DNS activity has
significantly reduced the time it takes to identify and resolve
issues. The reports are easily comprehensible, providing the
exact detail needed for our team to take effective action. We are
delighted with TCPWave's DDI reporting capabilities, which have
exceeded our expectations.
TCPWave's DDI reporting capabilities
have revolutionized our organization's performance. The swift
generation of customized reports on DHCP and DNS activity has
significantly reduced the time it takes to identify and resolve
issues. The reports are easily comprehensible, providing the
exact detail needed for our team to take effective action. We are
delighted with TCPWave's DDI reporting capabilities, which have
exceeded our expectations.